It was expected, however, that cybercriminals take advantage of this opportunity to infect the players and their devices. This time, the cybercriminals created a dangerous ransomware, with the same name of the game, attacking Windows accounts. A new ransomware which was dubbed as ‘Hidden-Tear’ ransomware that impersonates a Pokemon Go application for Windows. The security researcher Michael Gillespie found that there is a malware application for Windows that impersonates the Pokémon GO and targets the victims. The modus operandi is traditional. Once the computer is infected, the ransomware starts encrypting all the files with the following extensions: “.txt, .rtf, .doc, .pdf, .mht, .docx, .xls, .xlsx, .ppt, .pptx, .odt, .jpg, .png, .csv, .sql, .mdb, .sln , .php, .asp, .aspx, .html, .xml, .psd, .htm, .gif, .png”
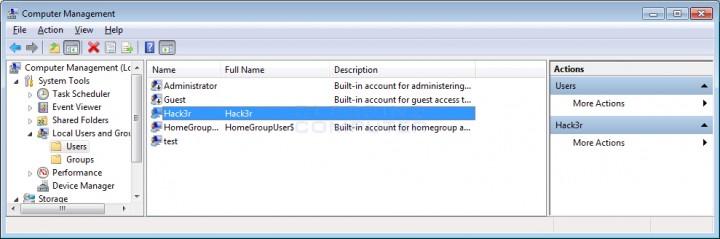
— Michael Gillespie (@demonslay335) August 12, 2016 The malware uses AES encryption to lock the files and then an extension of ‘.locked’ file in the affected documents will be added. Once the encryption process is complete, the ransomware will show a “rescue message” a file with this “هام جدا” ‘name. Txt’, requiring the victim to send an email to ‘[email protected]’ in order to get instructions for decryption. This is the redemption request message “(: Your files have been encrypted, descramble the Falaksa Mobilis following this address [email protected] and thank you in advance for your generosity” Seeming to have a “normal” behavior for this type of attack, as if it were a common ransomware then simply it encrypts files and asks money to decrypt. However, this brings something else up in the sleeve. In the process of machine infection, the malware creates itself a backdoor administrator account in Windows, with the name “Hack3r” and thus the malware operator will always have access to the victim’s computer. The work still goes further, because all traces of the account of creation are hidden using the Windows registry. The Pokemon GO ransomware will try to go to other machines for the infection and to spread itself by copying the ransomware executable to all removable drives. An “autorun.inf” file will be created, to make sure that the ransomware will be activated all the time whenever that contaminated unit is connected to a computer. “[AutoRun] OPEN = PokemonGo.exe ICON = PokemonGo.exe” Finally, it will also set up a copy of ransomware to other fixed drives on the computer, which will set another autorun file to start it whenever the computer is started. Despite of these capabilities, ransomware is still reportedly in the development phase. On the one hand, the malware uses a static AES key “123vivalalgerie” and its server uses an IP address that is intended for private use, which makes it impossible to reach via the internet. “private string TargetURL = “http://10.25.0.169/PokemonGo/write.php?info=”;” As we told earlier that the technique is still in early stages and quickly can encourage other hackers to reprogram and increase the damage capacity of this new type of ransomware.